Secure Collaboration for Microsoft 365
Secure collaboration for Microsoft 365 — control who can access, what they can do, and what happens after download.
See it in Action
Make the Secure Way the Easy Way—Eliminate Workarounds Inside Microsoft 365
When collaboration tools are too restrictive, people create workarounds—personal drives, unsecured chats, forwarded attachments. That’s how leaks happen. Govern 365 makes the secure way the easy way by enforcing protection directly inside your Microsoft 365 tenant.Trusted by deal teams & security officers | Audit-ready logs | Role-based access | Fast setup
What Is “Secure Collaboration”?
Secure collaboration is how organizations share sensitive information with external parties – partners, auditors, investors, suppliers, bidders – without losing control of what happens to the content once it’s shared. It replaces consumer file-sharing tools, generic portals, and email attachments with a controlled environment where access is bound to verified identity, permissions are explicit, and protection travels with every file.

Most secure collaboration tools create a separate silo – a new portal, a new login, a new place for sensitive data to live. Govern 365 works the other way around. Secure collaboration runs natively inside your Microsoft 365 tenant, using the Entra ID identity, Purview protection, and SharePoint storage you’ve already licensed. The secure path becomes the familiar path.
Secure Collaboration Benefits for Microsoft 365
Secure Collaboration Without Compromise in Microsoft 365 – External Access, DRM Protection & Full Audit Control

Compromise-Free Collaboration
User speed and data security, not one or the other.

Identity bound external access
Guests authenticate with their own corporate identity. No new accounts.

Protection Beyond Download
Microsoft Purview DRM enforces rights wherever the file travels.

Permission clarity
See and fix overexposure before it becomes an incident.

View Only enforcement
Block printing and copy/paste. Deter screenshots. Enforce per-document.

Evidence & response
Immutable audit logs support investigation and regulator review.
Complete Control Over Collaboration
Guest Access
Invite partners and suppliers using their existing corporate identity. Reduce onboarding friction while preserving auditability.
Membership Management
- Add/remove members in bulk
- Assign granular roles (Owners, Visitors)
- Sync across Teams & SharePoint
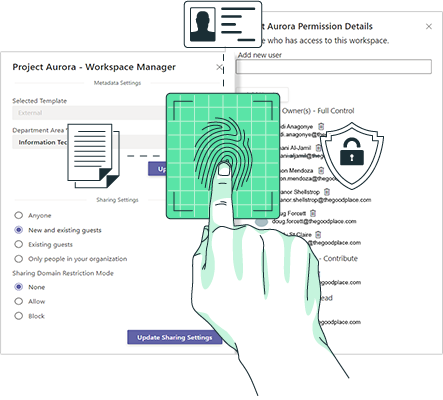
Permissions Analyzer
Gain total visibility into your least‑privilege posture with real‑time analysis.
- Visualize folder-level access maps
- Detect accidental overexposure
- Fix permission drift instantly
DRM Protection
- Block unauthorized forwarding
- Rights enforced after download
- Instant revocation of access
Fenced Secure Viewer
- Prevent printing & screenshots
- Advanced user-specific watermarking
- Block copy/paste functionality
Redaction
Remove or mask sensitive content before external sharing – without creating unmanaged copies or messy versioning.
NDA (Entry Gate)
Require digital acknowledgment before access and keep a fully auditable record of acceptance for compliance.
How It Works
Establish Identity
Guests authenticate with their corporate identity. Access is identity bound.
Apply Guardrails
Roles and permissions are set consistently, with visibility through the permissions analyzer.
Enforce Controls + Prove
DRM + viewer restrictions + watermarking apply where needed. Activity is logged and exportable.

Why Move Data to a “Black Box” Cloud?
Your CISO already invested in Microsoft security. Every time you use a third‑party collaboration tool or portal, you create a new attack surface by exfiltrating data.
Request a Security Deep DiveGovern 365 keeps collaboration native:
Zero‑Knowledge posture
You own the data and the keys. We never touch your raw content.
Tenant‑resident enforcement
Controls apply where work happens – directly within your environment.
Modern security expectations
Identity‑anchored access + durable protection + auditable activity.
Secure Collaboration Use Cases in Microsoft 365

Supplier Collaboration
Protect IP across the supply chain without credential chaos.

Legal & Compliance Discovery
Centralize sensitive exchanges with defensible controls.

Boardroom Communication
Secure board packs with view only and watermarking.

Product Development
Protect R&D and designs with durable controls and clear accountability.
Make secure collaboration the default—native to Microsoft 365.
Proof Points
- Identity‑bound external access (no new accounts)
- Durable protection after download (DRM)
- View‑only enforcement for the highest‑risk documents
Frequently Asked Questions
No. External partners – bidders, auditors, investors, suppliers – authenticate with their own corporate identity through Microsoft Entra ID B2B. No new accounts, no new passwords, no additional Microsoft license cost on your side. For guests whose organizations block cross-tenant sharing, the Vault portal provides brokered access without requiring any Microsoft 365 license.
Microsoft Purview DRM encrypts the file and binds it to a rights policy – view, edit, print, forward – that’s enforced wherever the file travels. A forwarded file that lands in an unauthorized inbox won’t open. Rights can be revoked centrally even after the file is distributed, so access changes the moment your policy changes.
Yes. The secure viewer blocks printing, disables copy and paste, and applies dynamic watermarks carrying the viewer’s identity, timestamp, and IP address to deter screenshots. View-only enforcement applies per folder or per document based on policy – use it for the highest-risk content and allow downloads for everything else.
No. Secure collaboration in Govern 365 is a reusable control layer for any high-stakes external sharing – supplier IP exchanges, board pack distribution, legal discovery, audit coordination, investor relations, and regulatory submissions. M&A due diligence is one high-volume use case among many. The same controls apply to every scenario.
Govern 365 uses SharePoint and Microsoft Purview as the foundation – we don’t replace them. What we add is the external-collaboration control layer on top of Microsoft 365: terms-of-access gates, fence visibility between bidder groups, a permissions analyzer that catches overexposure before invites go out, and immutable audit trails formatted for regulator review. For internal-only collaboration, sensitivity labels may be enough. For external sharing at scale, you’ll hit their limits quickly.
The permissions analyzer simulates any user’s view of the room before the invitation goes out – exactly what they’d see, what they could open, what actions they could take. Most accidental data leaks happen because someone was added to a folder that inherited broader permissions than anyone intended. The analyzer surfaces these cases before they become incidents. See Access Control Management
Every access-relevant action – views, downloads, permission changes, NDA acceptances, redactions, watermark renders, fence-group changes, failed login attempts – is captured in an immutable, tamper-evident audit log. Entries can’t be edited or deleted, and the sequence is cryptographically chained so alterations are detectable. Exports are ready for regulator or internal review in Excel, PDF, or structured formats. See Audit and Records Management
The full Secure Collaboration capability set – access control, granular permissions, watermarking, DRM, audit logs – is included starting with Founder Edition at $2,400/year. Advanced features scale with edition: fence visibility on Corporate and Enterprise, AI-assisted redaction on all editions, NDA enforcement starting with Growth. See Pricing
Insights | Testimonial